Insider List Management
Manage both insider and project lists
Centrally control your permanent and project insider lists with our MAR Flow software. Devolve ownership of projects throughout the business, allowing project and list owners to create and update lists as required.
Problems we solve
We provide the tools to manage both your insider and project lists. With unlimited project lists, you can ensure that you are always able to keep your information up to date with changes made in real-time. Handle communication with your insiders through the same system.
Find out how our system can help you securely manage your insiders and communications.
Discover how you can automate the communication of key information, acknowledgements and requests, while knowing you have real-time up to date audit information and MAR reports.
Specifications
Business Process & Communications
MARflow
Admin onlyMARflow
Employee AccessPermanent insider lists/PDMRs
Unlimited project lists
Online clearance requests
Clearance request workflows for Company approvers
Online acknowledgements
Prompt employees to communicate their acknowledgement externally, to be recorded in the system.
Acknowledgement form presented within the system, with responses automatically captured and stored.
Assign project/list managers
Communications
A suite of standard templates alongside customizable email and message content to align with brand language.
Selection of ad-hoc, automatically triggered, and scheduled messaging.
On-screen messages for employees
Branding
Simple colour scheme and logo to match your corporate branding.
Reporting & Audit
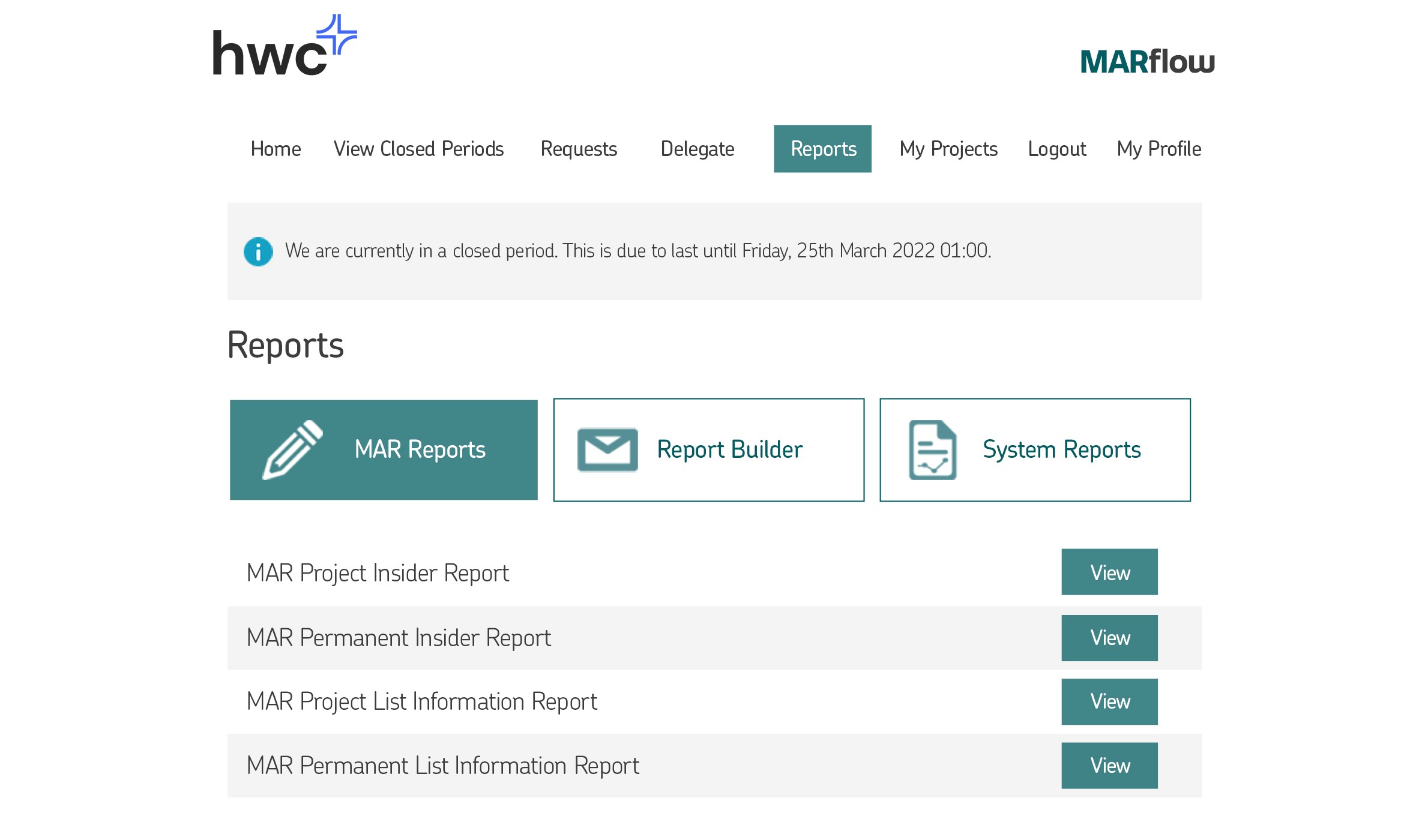
MAR reporting & audit report
Report builder tool
Frequently Asked Questions
Why work with us?
HWC has a rich history of successful systems for leading organizations around the world. We combine effective products with excellent and responsive service.
Where are the systems located?
Typically, the applications are hosted in London, UK. If there is a need for location-based data storage, then there are options to use data centres in the EU and US. There are also options for on premises (within your own corporate network) or within your own cloud space such as Azure.
Who uses your products?
Our applications are used by a wide range of organisations of all sizes, from FTSE 100 to private companies. The key factor tends to be an organisation which needs a system to complement, enhance and expand their activities, rather than having to re-design processes, inputs, and outputs to fit a system.
Will our data be safe?
Yes. Your data will be held in a secure environment, and you will control who has access to the system and the ability to enter and edit any data.